Different Types of Cyber Security & Tools

After the global pandemic disaster, the world got a major shift from office to online. This shift awakens the cyber security significance as much as ever before.
The unprecedented business shift encouraged many hackers to exploit network security. These days, hacking attempts become the most indiscernible reason to push users to pay special attention to cyber security.
In this blog, I will make you understand the cyber security concept first, and then will move on to its tools and types.
What is Cyber Security?
Cyber security can be defined as a practice of protecting an online network. There are certain tools involved that defend your servers, devices, and personally identifiable information. In short, you can say that cyber security is the mix of technologies to protect a network, system, devices, and confidential data of businesses and individuals.
Why is Cyber Security Significant?
When it comes to the significance of cyber security, then we can witness that it is the largest growing domain after the COVID-19 crisis.
Practically, businesses and users are more into cyberspace and pairing accounts with different social platforms every day. It is increasing the risk of cyber attacks on personal data. In fact, many cyber attacks have taken place during the COVID-19 crisis.
A few of the most widely attempted cyber-attacks are DDoS on gaming platforms, social engineering scams, sophisticated phishing, ransomware, and malware attacks.
Cyber security is indispensable to fight and defend systems against such hacking attacks. It is crucial to understand and implement cyber security for network protection.
Companies must train employees regarding cyber security implementation and importance because it is the best way to prevent a system from unauthorized access.
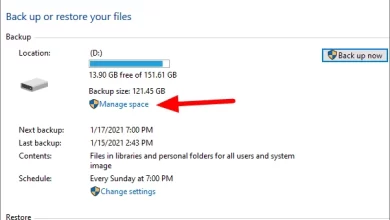
What Are the Cyber Security Tools

There are various tools available to meet cyber security needs. Depending on an organization’s security level, different security tools can be used. For example, a large organization will need hardware VPN to protect its network from intruders. Similarly, a medium or small size company can use a software VPN for protecting its network.
Below, I will outline some cyber security software/tools that are mostly used by businesses for network defense.
Antivirus Software
Antivirus software is the best tool for cyber defense. It detects malicious sources like infected links and websites and blocks them before damaging your device. Antivirus software also fights against the latest threats that may harm your system.
Firewall
A Firewall is another essential cyber security solution that filters your network traffic and protects the system from irregular connection attempts. It stops unauthorized access from entering into a system in this way. Your computer gets an added layer of protection against cyber attacks.
VPN (Virtual Private Network)
Virtual private networks are one of the best security tools for network protection. VPNs use end-to-end bit 256 encryption that hides your traffic, so no one can read it. A VPN also assigns you its server-based IP address. It means that no intruders can see your IP address nor trace your actual location.
Password Managers
Password managers are an essential cyber security tool because it lets you be able to quickly use a new password for different accounts. It is not advised to use the same password for various accounts. In case, if your password gets hacked, then you will compromise data security for all your accounts. Therefore, it is important to use a password manager for password protection.
PKI
PKI is also a secure technology. It refers to the public key infrastructure. Together with SSL or TLS, PKI better encrypts servers’ communication and maintains the HTTPS browser address bar padlock.
Now, you have understood what cyber security is, why it is considerable, and what tools can be a part of your cyber security plan. It’s time to have a look at the cyber security types:
Types of Cyber Security
Application security
Application security mainly focuses on applications and utilized different cyber security tools to protect applications from unwanted access. This security uses several components including, antivirus software, Firewalls, and encryption software, to stop intruders from damaging a device or application.
Network Security
Just like Application security, Network security also uses multiple approaches to prevent unauthorized network access. Network administration and the entire IT teams keep implementing different security approaches to monitor and control traffic.
Network engineers incessantly deploy Firewalls, encryptions, two-factor authentication, new passwords, and other security policies to prevent unnecessary network intervention.
IoT Security
IoT or internet of things referred to the smart internet-connected devices. Such devices are more vulnerable and if fall victim to the data breach, then data loss will be huge. Strong encryption for Wi-Fi is required for IoT protection.
A VPN router is also important to protect the network for smart internet-connected devices. Other than Wi-Fi protection and a VPN enabled router, checking a device’s default settings is also important.
Cloud Security
Cloud security is also a type of cyber security. It involves multiple software tools to secure and monitor data within cloud applications. New security tools are continuously evolving to better protect cloud data.
There are the latest apps for cloud protection, among which the two most common cloud security apps are CipherCloud and OKta.
Conclusion
I hope that you have found this article helpful and understood what cyber security is, what are its tools and types, and why cyber security is crucial. These days’ cyber attacks are emerging like never before. Therefore, there have to be smart tools to defend your network. Implementing the latest cyber security method is the only way to keep your network secure.